C# Advanced Features: Architecture Patterns and Decision Framework (2025)
Introduction
Mastering programming languages and their ecosystems is fundamental to modern software engineering. Each language brings unique paradigms, performance characteristics, and tooling that shape how developers solve problems. Understanding multiple languages broadens your architectural perspective and enables you to choose the right tool for each challenge.
This guide explores C Advanced Features in depth, covering the foundational concepts, practical patterns, and professional practices that separate hobby code from production-grade software. Whether you're solidifying your understanding or adopting advanced techniques, this article provides actionable knowledge for 2025.
Why C Advanced Features Matters
Modern software development demands more than just writing code that works. C Advanced Features addresses critical aspects of professional development:
- Code Quality: Write maintainable, readable code that teams can work with confidently
- Reliability: Build systems that handle edge cases, failures, and unexpected input gracefully
- Performance: Understand when and how to optimize without sacrificing clarity
- Collaboration: Follow patterns and conventions that enable effective teamwork
- Security: Write code that resists common vulnerabilities and attack vectors
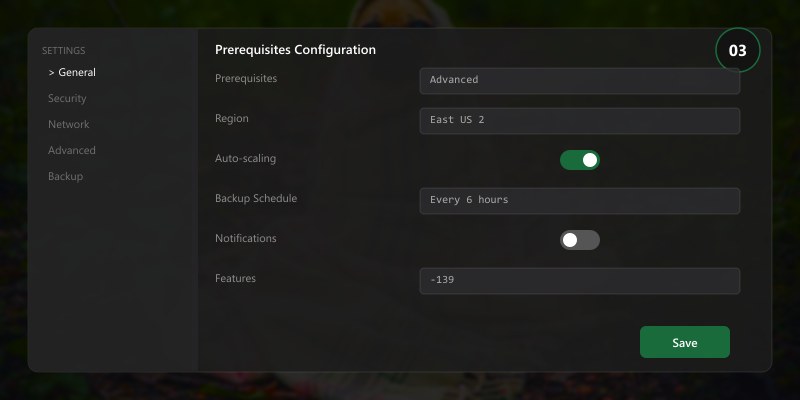
Prerequisites
- Development environment with appropriate compiler/interpreter
- Code editor or IDE with language support (VS Code recommended)
- Package manager for the target ecosystem
- Version control with Git 2.40+
- Understanding of core computer science concepts
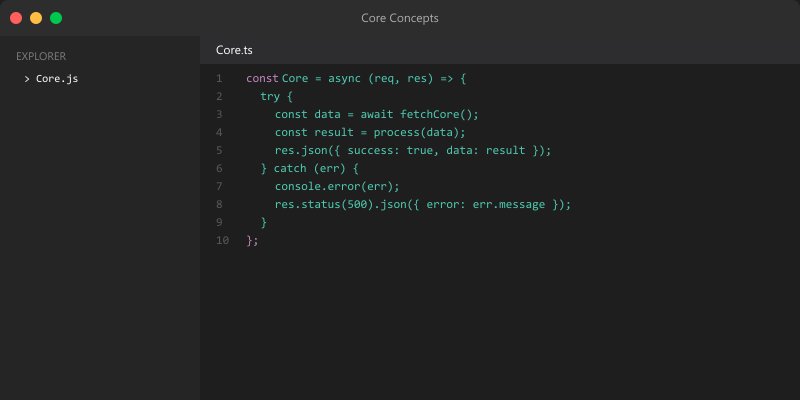
Core Concepts
Concept 1: Clean Code Structure
Well-structured code follows the principle of least surprise — each module, function, and variable does what its name suggests:
// Clean structure example
class DataProcessor {
constructor(validator, transformer, repository) {
this.validator = validator;
this.transformer = transformer;
this.repository = repository;
}
async process(rawData) {
// Validate input
const validationResult = this.validator.validate(rawData);
if (!validationResult.isValid) {
throw new ValidationError(validationResult.errors);
}
// Transform to internal format
const transformedData = this.transformer.transform(rawData);
// Persist and return
const saved = await this.repository.save(transformedData);
return { success: true, data: saved };
}
}
Concept 2: Error Handling Patterns
Production code must handle errors explicitly and informatively:
from dataclasses import dataclass
from typing import TypeVar, Generic
T = TypeVar('T')
@dataclass
class Result(Generic[T]):
success: bool
data: T | None = None
error: str | None = None
@classmethod
def ok(cls, data: T) -> 'Result[T]':
return cls(success=True, data=data)
@classmethod
def fail(cls, error: str) -> 'Result[T]':
return cls(success=False, error=error)
def divide(a: float, b: float) -> Result[float]:
if b == 0:
return Result.fail("Division by zero")
return Result.ok(a / b)
# Usage
result = divide(10, 3)
if result.success:
print(f"Result: {result.data:.2f}")
else:
print(f"Error: {result.error}")
Concept 3: Testing Strategies
import { describe, it, mock } from 'node:test';
import assert from 'node:assert/strict';
describe('DataProcessor', () => {
it('should process valid data successfully', async () => {
const processor = new DataProcessor(
{ validate: () => ({ isValid: true }) },
{ transform: (d) => ({ ...d, transformed: true }) },
{ save: mock.fn(async (d) => ({ id: 1, ...d })) }
);
const result = await processor.process({ name: 'test' });
assert.equal(result.success, true);
assert.equal(result.data.transformed, true);
});
it('should reject invalid data', async () => {
const processor = new DataProcessor(
{ validate: () => ({ isValid: false, errors: ['Bad data'] }) },
{ transform: () => {} },
{ save: () => {} }
);
await assert.rejects(
() => processor.process({ bad: true }),
{ name: 'ValidationError' }
);
});
});
Best Practices
- Follow SOLID Principles: Single responsibility, open/closed, Liskov substitution, interface segregation, dependency inversion
- Write Tests First (or Alongside): Tests serve as living documentation and prevent regressions
- Handle Edge Cases: Empty collections, null values, concurrent access, network failures
- Profile Before Optimizing: Use profiling tools to find real bottlenecks, not assumed ones
- Review Code Regularly: Fresh eyes catch issues automated tools miss
- Keep Dependencies Current: Regular updates prevent security vulnerabilities from accumulating
- Document Why, Not What: Code shows what happens; comments should explain why
Common Pitfalls
| Pitfall | Impact | Prevention |
|---|---|---|
| Swallowed errors | Silent failures, data loss | Always log or return errors explicitly |
| Missing input validation | Security vulnerabilities | Validate at every system boundary |
| Premature optimization | Complex, hard-to-maintain code | Profile first, optimize measured bottlenecks |
| Tight coupling | Difficult to test and change | Use dependency injection and interfaces |
| Inconsistent naming | Confusion, maintenance burden | Enforce conventions with linting tools |
Architecture Decision and Tradeoffs
When designing software development solutions with Programming Languages, consider these key architectural trade-offs:
| Approach | Best For | Tradeoff |
|---|---|---|
| Managed / platform service | Rapid delivery, reduced ops burden | Less customisation, potential vendor lock-in |
| Custom / self-hosted | Full control, advanced tuning | Higher operational overhead and cost |
Recommendation: Start with the managed approach for most workloads and move to custom only when specific requirements demand it.
Validation and Versioning
- Last validated: April 2026
- Validate examples against your tenant, region, and SKU constraints before production rollout.
- Keep module, CLI, and SDK versions pinned in automation pipelines and review quarterly.
Security and Governance Considerations
- Apply least-privilege access using RBAC roles and just-in-time elevation for admin tasks.
- Store secrets in managed secret stores and avoid embedding credentials in scripts or source files.
- Enable audit logging, data protection policies, and periodic access reviews for regulated workloads.
Cost and Performance Notes
- Define budgets and alerts, then monitor usage and cost trends continuously after go-live.
- Baseline performance with synthetic and real-user checks before and after major changes.
- Scale resources with measured thresholds and revisit sizing after usage pattern changes.
Official Microsoft References
- https://learn.microsoft.com/
- https://learn.microsoft.com/azure/
- https://learn.microsoft.com/power-platform/
- https://learn.microsoft.com/microsoft-365/
Public Examples from Official Sources
- These examples are sourced from official public Microsoft documentation and sample repositories.
- Documentation examples: https://learn.microsoft.com/training/
- Sample repositories: https://github.com/microsoft
- Prefer adapting these examples to your tenant, subscriptions, and governance requirements before production use.
Key Takeaways
- ✅ C Advanced Features skills are foundational for professional software development
- ✅ Clean code structure and explicit error handling prevent the most common production issues
- ✅ Testing at multiple levels catches different categories of bugs
- ✅ Performance optimization should be data-driven, not assumption-driven
- ✅ Security awareness must be embedded in every phase of development
Additional Resources
Part of our 2025 Programming Languages series on professional development practices.
