Azure Storage & Databases: Architecture Patterns and Decision Framework (2026)
Introduction
Microsoft Azure continues to evolve as a leading cloud platform, offering over 200 services spanning compute, storage, networking, AI, and DevOps. Organizations worldwide rely on Azure for mission-critical workloads, benefiting from its global infrastructure of 60+ regions, enterprise-grade security, and deep integration with the Microsoft ecosystem.
This article establishes the architectural foundation for Azure Storage Databases, providing the decision frameworks, design patterns, and evaluation criteria you need to make informed technology choices. We analyze tradeoffs between different approaches, define selection criteria for common scenarios, and present reference architectures that serve as starting points for your own implementations.
Series Context: This is Part 1 of the Azure Storage Databases specialized series. Part 2 covers hands-on implementation, and Part 3 addresses production operations and optimization.
Business Context and Value Proposition
Before diving into architecture, it's essential to understand the business drivers:
Business Objectives
| Objective | How Azure Storage Databases Addresses It | Measurable Outcome |
|---|---|---|
| Reduce operational costs | Automation and resource optimization | 25-40% cost reduction |
| Improve time-to-market | Standardized patterns and reusable components | 50% faster deployments |
| Enhance security posture | Defense-in-depth with automated compliance | Zero critical vulnerabilities |
| Increase reliability | Redundancy, failover, and self-healing | 99.95% uptime SLA |
| Enable scalability | Elastic architecture with auto-scaling | Handle 10x traffic spikes |
Stakeholder Analysis
Understanding who benefits from Azure Storage Databases informs architectural decisions:
- Executive Leadership: ROI visibility, risk reduction, competitive advantage
- IT Operations: Reduced toil, automated runbooks, proactive monitoring
- Development Teams: Faster iteration, consistent environments, self-service capabilities
- Security & Compliance: Audit trails, automated policy enforcement, incident response
- End Users: Better performance, reliability, and feature velocity
Architecture Patterns
Pattern 1: Centralized Management
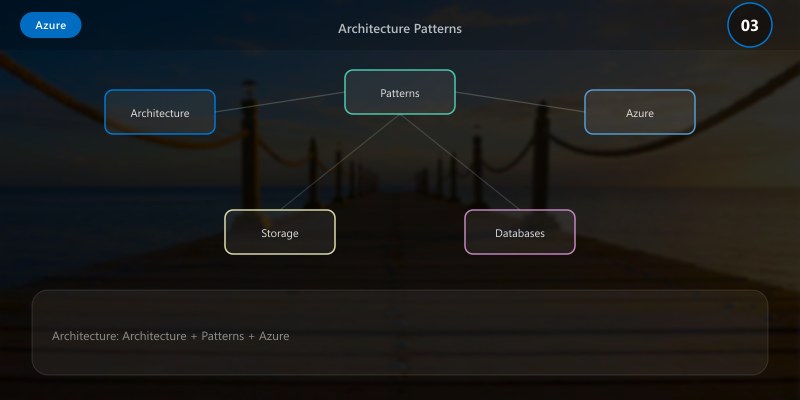
This pattern consolidates Azure Storage Databases management into a single control plane with distributed execution.
When to Use:
- Organizations with a strong central IT team
- Regulatory requirements mandating centralized oversight
- Environments requiring consistent policy enforcement across all resources
Architecture:
Architecture Overview: Central Management Plane
Tradeoffs:
- ✅ Consistent governance and policy enforcement
- ✅ Simplified compliance reporting
- ⚠️ Single point of failure if control plane is unavailable
- ⚠️ Potential latency for distributed teams
Pattern 2: Federated Architecture
This pattern distributes ownership while maintaining organizational standards through shared guardrails.
When to Use:
- Multi-team organizations with autonomous product teams
- Environments where teams need flexibility within boundaries
- Global deployments requiring regional sovereignty
Architecture:
Architecture Overview: Shared Platform (Guardrails Layer)
Tradeoffs:
- ✅ Team autonomy and faster decision-making
- ✅ No single point of failure
- ⚠️ Risk of inconsistency across teams
- ⚠️ More complex to audit and govern
Pattern 3: Hybrid Layered Architecture
Combines centralized governance with team-level operational freedom. This is the most common pattern for medium-to-large enterprises.
When to Use:
- Most enterprise organizations
- Environments balancing innovation speed with compliance
- Organizations transitioning from centralized to more autonomous models
Decision Framework
Use this framework to select the right architecture pattern:
Decision Matrix
| Factor | Centralized | Federated | Hybrid |
|---|---|---|---|
| Team autonomy | Low | High | Medium |
| Governance strength | High | Medium | High |
| Implementation complexity | Low | Medium | High |
| Scalability | Medium | High | High |
| Compliance ease | High | Low | High |
| Time to implement | Fast | Medium | Slow |
| Long-term maintainability | Medium | Medium | High |
Decision Tree
Is regulatory compliance a primary driver?
- Yes → Lean toward Centralized or Hybrid
- No → All patterns viable
Do you have >5 autonomous product teams?
- Yes → Federated or Hybrid
- No → Centralized or Hybrid
Is the organization ready for platform engineering?
- Yes → Hybrid (recommended)
- No → Centralized (start simple, evolve later)
Technology Selection Criteria
Evaluation Scorecard
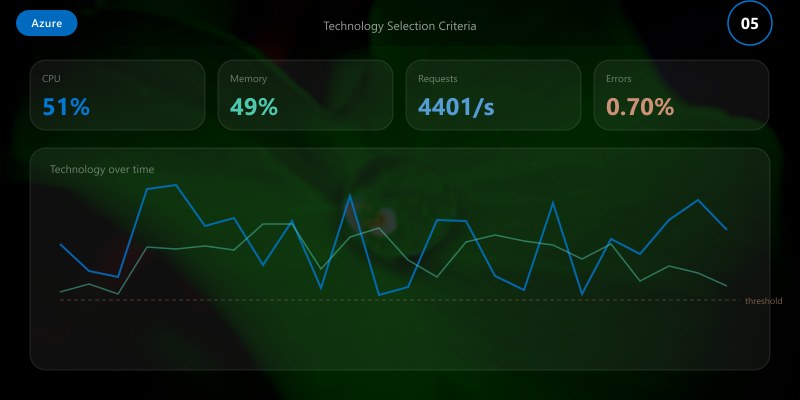
When evaluating specific technologies for your Azure Storage Databases implementation, score each option across these dimensions:
| Criterion | Weight | How to Assess |
|---|---|---|
| Maturity & Stability | 25% | GA status, version history, known issues |
| Integration Ecosystem | 20% | Connector count, API quality, SDK support |
| Security & Compliance | 20% | Certifications, encryption, audit capabilities |
| Performance & Scale | 15% | Benchmarks, scaling model, latency guarantees |
| Cost Model | 10% | TCO analysis, pricing predictability |
| Team Skills | 10% | Learning curve, documentation quality, community |
Reference Architecture
The following reference architecture represents our recommended starting point for most organizations:
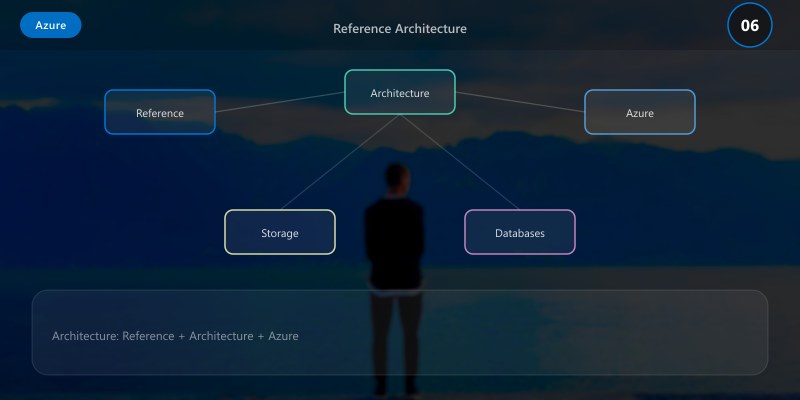
{
"architecture": {
"name": "Azure Storage Databases Reference Architecture",
"version": "1.0",
"pattern": "hybrid-layered",
"components": {
"governance": {
"policies": "Automated policy-as-code enforcement",
"compliance": "Continuous compliance monitoring",
"cost_management": "Budget alerts and optimization recommendations"
},
"platform": {
"identity": "Centralized identity with SSO and MFA",
"networking": "Hub-spoke topology with private endpoints",
"monitoring": "Unified observability across all components",
"security": "Defense-in-depth with zero-trust principles"
},
"workloads": {
"compute": "Right-sized with auto-scaling policies",
"data": "Encrypted at rest and in transit, geo-redundant",
"integration": "Event-driven with guaranteed delivery"
}
},
"non_functional_requirements": {
"availability": "99.95% SLA",
"rto": "4 hours",
"rpo": "1 hour",
"throughput": "1000 requests/sec baseline"
}
}
}
Risk Assessment
| Risk | Probability | Impact | Mitigation |
|---|---|---|---|
| Vendor lock-in | Medium | High | Abstract dependencies, use managed standards |
| Skill gaps | High | Medium | Training investment, documentation, pair programming |
| Cost overrun | Medium | Medium | Budget alerts, right-sizing reviews, reserved capacity |
| Security breach | Low | Critical | Zero-trust, encryption, automated threat detection |
| Performance issues | Medium | High | Load testing, capacity planning, auto-scaling |

Migration Considerations
If you're migrating from an existing implementation:
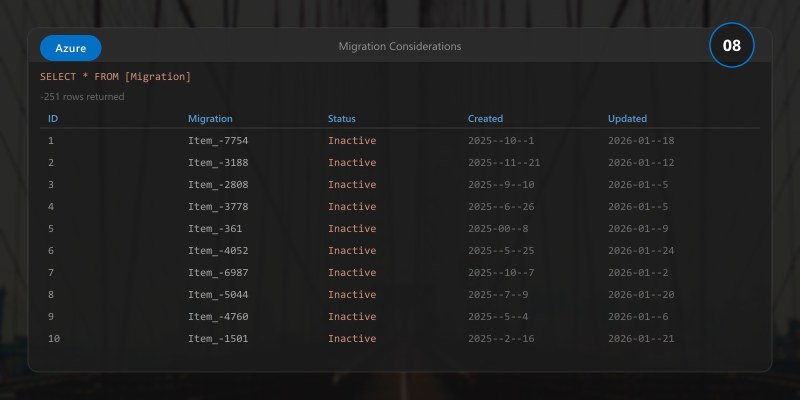
- Assess Current State: Document existing architecture, dependencies, and pain points
- Define Target State: Map to the reference architecture with organization-specific adjustments
- Plan Migration Waves: Group components by dependency and risk for phased migration
- Establish Rollback Procedures: Every migration step must have a documented rollback plan
- Run Parallel: Operate old and new systems simultaneously during transition periods
Architecture Decision and Tradeoffs
When designing cloud infrastructure solutions with Azure, consider these key architectural trade-offs:
| Approach | Best For | Tradeoff |
|---|---|---|
| Managed / platform service | Rapid delivery, reduced ops burden | Less customisation, potential vendor lock-in |
| Custom / self-hosted | Full control, advanced tuning | Higher operational overhead and cost |
Recommendation: Start with the managed approach for most workloads and move to custom only when specific requirements demand it.
Validation and Versioning
- Last validated: April 2026
- Validate examples against your tenant, region, and SKU constraints before production rollout.
- Keep module, CLI, and SDK versions pinned in automation pipelines and review quarterly.
Security and Governance Considerations
- Apply least-privilege access using RBAC roles and just-in-time elevation for admin tasks.
- Store secrets in managed secret stores and avoid embedding credentials in scripts or source files.
- Enable audit logging, data protection policies, and periodic access reviews for regulated workloads.
Cost and Performance Notes
- Define budgets and alerts, then monitor usage and cost trends continuously after go-live.
- Baseline performance with synthetic and real-user checks before and after major changes.
- Scale resources with measured thresholds and revisit sizing after usage pattern changes.
Official Microsoft References
- https://learn.microsoft.com/azure/
- https://learn.microsoft.com/azure/architecture/
- https://learn.microsoft.com/azure/well-architected/
Public Examples from Official Sources
- These examples are sourced from official public Microsoft documentation and sample repositories.
- Documentation examples: https://learn.microsoft.com/azure/architecture/
- Sample repositories: https://github.com/Azure-Samples
- Prefer adapting these examples to your tenant, subscriptions, and governance requirements before production use.
Key Takeaways
- ✅ Architecture decisions should be driven by business objectives, not technology preferences
- ✅ The hybrid layered pattern works for most enterprise organizations
- ✅ Use the decision framework to systematically evaluate options
- ✅ Security and compliance must be designed in, not bolted on
- ✅ Plan for evolution — good architecture accommodates change
What's Next
In Part 2: Implementation Blueprint, we'll take this architecture and build it step-by-step with hands-on walkthroughs, code samples, and validation checkpoints.
Additional Resources
- Microsoft Learn - Azure Fundamentals
- Azure Architecture Center
- Azure CLI Reference
- Azure Pricing Calculator
This is Part 1 of the Azure Storage Databases specialized series (2026). Continue with the Implementation Blueprint for hands-on guidance.
